By Olivia Dubois
·
April 20, 2026
Shadow IT is technology adopted without IT validation: SaaS, cloud storage, personal devices, and generative AI tools like ChatGPT. It often starts as productivity — but without visibility it becomes systemic risk.
A sobering signal: some industry reporting suggests ~11% of content pasted into consumer GenAI tools can include sensitive material — which means uncontrolled egress if policies aren’t enforced.
Platforms like Avanoo combine discovery, risk scoring, and user guidance so you can see, prioritize, and remediate without pretending Shadow IT doesn’t exist.
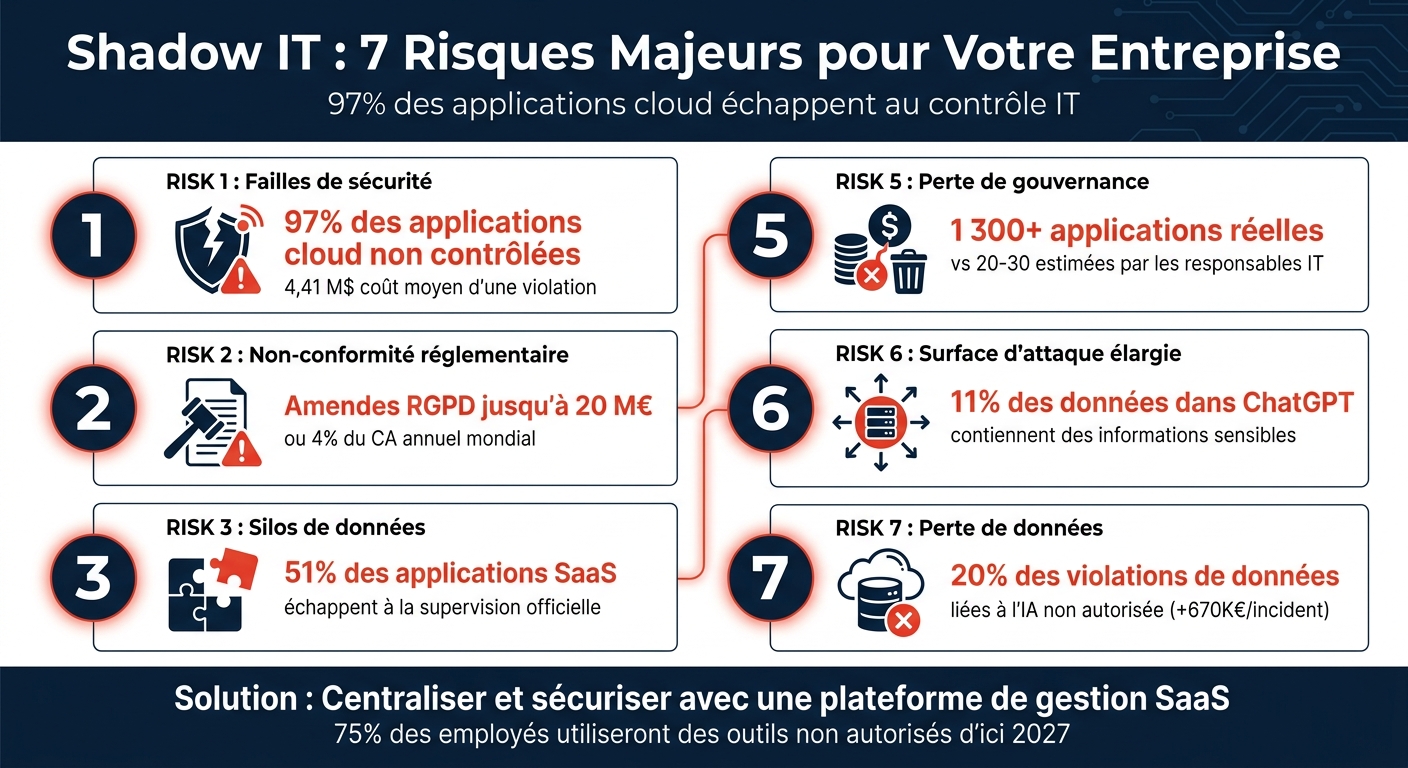
Shadow IT creates blind spots: studies commonly cite that the majority of enterprise cloud apps are not fully governed. Misconfigurations and missing controls turn into incidents — cloud configuration errors have been associated with breach costs averaging ~$4.41M in public research.
GenAI compounds the issue: security leaders frequently report widespread use of unapproved AI tools, and sensitive snippets can leave your controlled perimeter once pasted into a consumer model.
"You can't protect what you can't see." — CrowdStrike
Unsanctioned apps also miss enterprise patch cadence — leaving known CVEs exploitable for longer.
If you can’t inventory tools, you can’t prove GDPR, NIS2, or sector controls. Shadow stacks often store data outside the EU without proper transfer mechanisms.
"Shadow IT isn’t always malicious — but you still need guardrails to protect the brand." — Nick Hartman, Western Governors’ University
When regulation changes, unsanctioned apps are the last to be updated — creating “frozen” non-compliance.
Teams adopt Trello, Asana, personal Dropbox or Google Drive — and the system of record fragments. Finance sees one KPI set; operations sees another.
"If information stays scattered across Shadow IT silos, future AI initiatives lack the context to produce reliable outcomes." — Hyland
When people leave, data can remain in unsanctioned tenants — outside legal hold and backups.
Decentralized buying creates overlapping tools and impossible renewal calendars. Shadow-related incidents also pull senior engineers into forensic work — the most expensive “support ticket” you can generate.
"The result is wasted time, money, and resources as the organization struggles to maintain disparate systems." — Proofpoint
IT estimates tens of unsanctioned apps; audits often find hundreds to thousands. Without a living inventory, access reviews and incident response start from a false map.
"Shadow IT makes IT lose control of how data is managed." — Margot Guicheteau, Pleo
AI programs suffer too: models need trusted, consolidated data — not 50 shadow spreadsheets.
Unsanctioned apps bypass corporate firewall policies, SIEM coverage, and MFA mandates. Lateral movement becomes easier when an attacker lands in a “low visibility” SaaS tenant employees connected to “just to move faster.”
"Every unsanctioned app or device becomes another place an attacker can push." — Guardian Digital
Pair technical controls with an AI acceptable use policy — people need clarity, not surprise blocks.
Shadow tools rarely integrate cleanly with official systems — duplicated records, broken workflows, and “unofficial” backups that don’t exist when ransomware hits.
"Unauthorized systems rarely integrate well with official tools — creating silos, duplicate data, and broken workflows." — Netscout
Unapproved GenAI can also accelerate accidental disclosure — treat it as data egress, not “just another website.”

Avanoo focuses on continuous discovery and guided remediation: see unsanctioned SaaS and AI, consolidate signals for security teams, and reduce duplicate spend. AI DLP-style signals help catch risky transfers early.
| Shadow IT risk | Business impact | How Avanoo helps |
|---|---|---|
| Security gaps | Breaches, unauthorized access | Real-time discovery + risk scoring |
| Compliance gaps | Fines, failed audits | Continuous controls evidence |
| Data silos | Fragmented reporting | Unified visibility across sources |
| Excess cost | Wasted budget | Duplicate + zombie license detection |
| Governance loss | Weak audit trails | Central inventory + ownership |
| Attack surface | More ingress paths | Detection of risky apps and flows |
| Data fragmentation | Backup gaps | Policy coverage across discovered apps |
Shadow IT is not a “people problem” isolated from security — it is how modern work happens unless procurement and security keep pace. The fix is not draconian blocking alone; it’s visibility + fast approvals + better defaults.
"Adopting a sovereign AI approach means knowing where data goes — and giving employees absolute transparency."
Centralizing SaaS governance improves security, optimizes SaaS spend, and makes compliance measurable instead of aspirational.
Inventory what employees use (SSO + expenses + endpoint/browser signals), compare to an approved catalog, and run continuous discovery — not annual surveys alone.
Unsupervised automation (“shadow AI decisions”) and pasting sensitive data into consumer tools. Most breaches still start with simple mistakes — not nation-state magic.
Discover first, then publish a short allow/deny guidance, offer approved alternatives, and use nudges in-product. Friction should land on true high-risk flows — not on every experiment.
Shadow AI Expert & Chief AI Officer
Olivia Dubois is Shadow AI Expert and Chief AI Officer at Avanoo. An HEC Paris graduate and former BCG consultant, she helps enterprises detect and govern Shadow AI and Shadow IT.
See how Avanoo can map your SaaS and AI landscape, reduce risk, and optimize costs. A reliable platform with dedicated human support.