By Tanguy Duthion
·
April 22, 2026
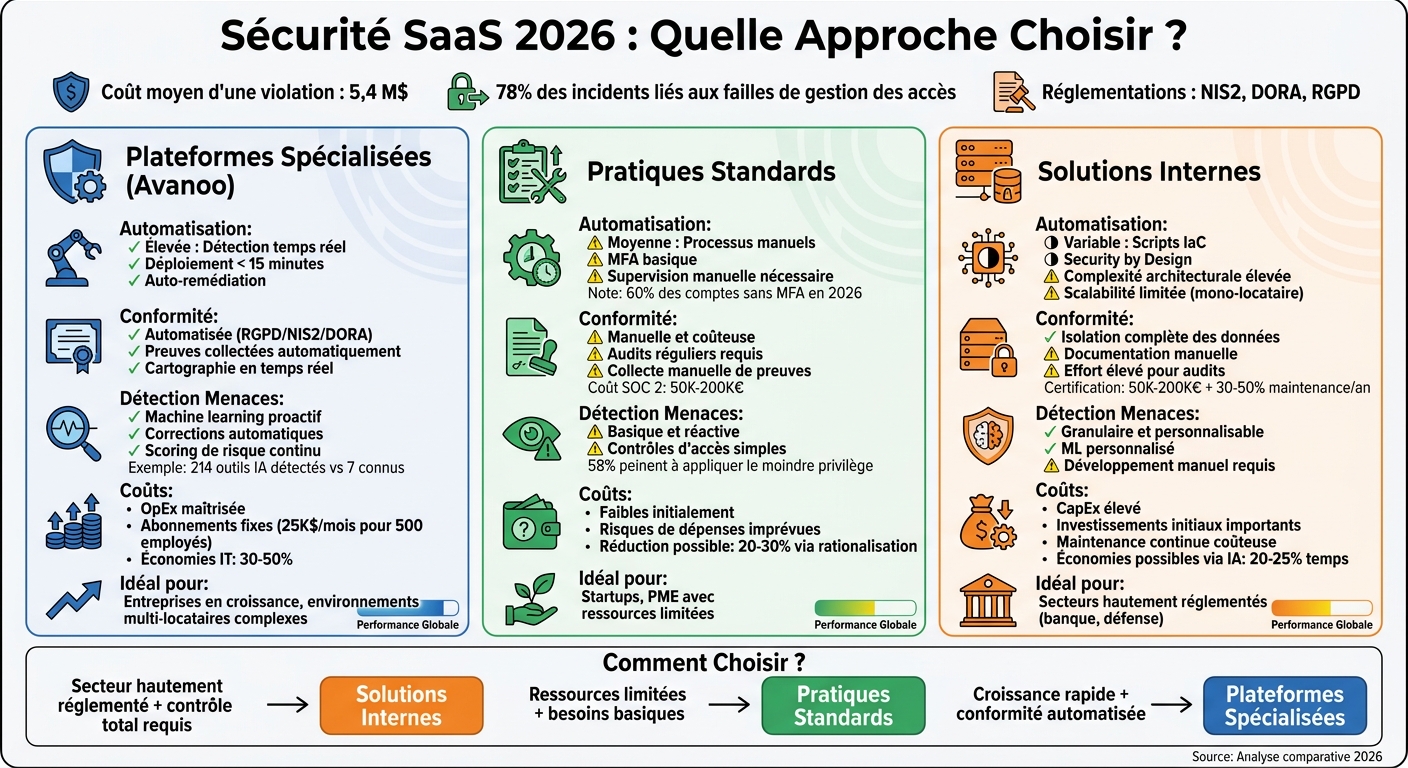
In 2026, SaaS security is a board-level topic: data breaches average $5.4M, and 78% of incidents still tie back to access management and weak multi-tenant isolation. With NIS2, DORA, and GDPR in force, teams usually pick one of three paths:
| Dimension | Specialized (e.g. Avanoo) | Standard practices | In-house |
|---|---|---|---|
| Automation | High — continuous discovery | Medium — mostly manual | Variable — depends on engineering |
| Compliance | Automated mapping to GDPR / NIS2 / DORA | Manual evidence collection | Precise, expensive to maintain |
| Threat response | ML-assisted drift detection + guided remediation | Mostly reactive alerts | Fine-grained, complex to operate |
| Cost model | Predictable OpEx + measurable savings | Low upfront, hidden breach risk | High CapEx + staffing |
The right choice depends on sector, risk appetite, and how fast your SaaS estate grows.

Avanoo is a European SaaS governance and security platform built for EU regulatory reality: data stays in-region (AWS eu-west-3), and the product is designed to help CISOs and IT leaders see what is actually used — including unsanctioned SaaS and generative AI tools.
You can connect identity (e.g. Okta, Microsoft Entra ID, Google Workspace), finance signals, and browser telemetry. That combination is how a 15,000-employee European bank found 214 active AI tools when IT only knew about 7 — an 8.65× visibility gap, as their security lead put it:
"We discovered 214 AI tools in use. We only knew about 7. Avanoo gave us the clarity to act."
In-product nudges steer people toward approved tools without blocking work outright — a practical bridge from “policy on paper” to “policy in the flow of work.”
Avanoo maps unsanctioned SaaS and Shadow AI usage, supplier relationships, and risky data flows. For sensitive environments, anonymous collection modes can reduce PII exposure while still surfacing risky domains and behaviors. A Big Four Paris CIO reported:
"Avanoo gave us full visibility into SaaS and AI usage, strengthened security, and helped us optimize costs."
For EU teams, this maps cleanly to expectations under NIS2 and DORA: know your assets, know your vendors, and prove continuous control — not a once-a-year spreadsheet exercise.
Real-time signals include misconfigurations, unusual data movement, and unapproved AI usage (e.g. ChatGPT, Claude). Browser extension coverage catches tools that never touch SSO. A CAC40 industrial CISO noted:
"With Avanoo, we identified and controlled unauthorized SaaS and AI, cutting compliance risk materially."
Beyond security, unused seats and duplicate tools are budget leaks. Avanoo’s positioning is simple: security and spend governance share the same inventory. Pricing varies by plan and scale; teams typically start with a time-boxed diagnostic before moving to continuous monitoring.
This path leans on SSPM (SaaS Security Posture Management) and broader SMP (SaaS Management Platform) capabilities: continuous configuration checks, drift detection, and compliance templates. It works — until tool sprawl outpaces manual review.
Good SSPM automates discovery and applies Zero Trust patterns (verify every request with context). DevSecOps shifts checks into CI/CD. Still, projections remain harsh: 60%+ of users may still lack MFA on some apps by 2026 if nobody operationalizes lifecycle management.
SOC 2 Type II, ISO 27001, GDPR, and the EU Data Act (in force September 2025) all push toward continuous control monitoring instead of annual “audit theater.” Certification is expensive (often €50k–€200k for a first SOC 2 program), but cheaper than a breach.
Standard tooling flags impossible travel, risky sharing, and mass downloads. Cloud detection and response can auto-remediate obvious issues (disable accounts, revoke risky shares). The gap is coverage: if Shadow IT bypasses sanctioned apps, SSPM alone may not see it.
Centralized SaaS management can recover 20–30% of waste through better renewal hygiene and license reclamation — if finance, IT, and security share one source of truth.
Defense, critical finance, and other highly regulated environments sometimes mandate full control: single-tenant architectures, bespoke logging, custom ML rules.
IaC security gates (Checkov, tfsec) catch misconfigurations early. The downside is scalability: single-tenant systems don’t autoscale like multi-tenant SaaS without serious platform engineering.
You can meet strict isolation requirements and build immutable audit trails — at the cost of velocity. For visibility across sanctioned and unsanctioned SaaS, many teams still add a discovery layer such as Discover.
Custom models can encode org-specific anomalies (e.g. impossible travel tailored to your travel policy). The tradeoff is maintenance: every new SaaS pattern is another rule set to own.
CapEx and headcount are higher, but GenAI-assisted SecOps (triage, questionnaire automation) can claw back time. Token/caching discipline also matters as AI security workflows grow.
| Dimension | Avanoo | Standard SaaS practices | In-house |
|---|---|---|---|
| Automation / scale | High — continuous discovery + guided remediation | Low–medium — manual processes dominate | Medium–high — depends on platform maturity |
| Compliance | Evidence automation aligned to EU frameworks | Manual audits; expensive drift | Strong control; heavy documentation burden |
| Threat detection | Proactive, user-guided, broad coverage (incl. non-SSO) | Reactive controls; blind spots on Shadow IT | Granular; costly to keep current |
| Cost | Predictable OpEx; savings from duplicates + seats | Lower upfront; breach tail risk | High build + run costs |
"CSPM turns compliance from a point-in-time exercise into an automated, continuous process."
— Ayi Nedjimi Consultants
By 2027, centralized automation will keep widening the efficiency gap. For most growing enterprises, a platform like Avanoo is the pragmatic middle path: fast time-to-value, continuous compliance posture, and coverage for tools employees actually use — not only the ones IT provisioned.
Adopt Zero Trust (verify every access), enforce MFA, tighten RBAC, and use row-level security where available. Combine technical controls with continuous discovery so “unknown SaaS” doesn’t become your default attack surface.
Blend network/DNS telemetry, expense signals, browser extension visibility, and lightweight employee surveys. CASB-style monitoring helps, but the winning pattern is multiple corroborating sources — SSO alone is insufficient for modern AI tools.
Track risk register freshness, incident SLAs, vendor criticality reviews, access reviews, and audit evidence automation rate. Pair KPIs with quarterly executive reviews — regulators and boards increasingly expect continuity, not snapshots.
Co-fondateur & CEO
Tanguy Duthion is co-founder and CEO of Avanoo. Previously at Google and Asana, he founded Avanoo to help organizations regain control over their SaaS and AI usage.
See how Avanoo can map your SaaS and AI landscape, reduce risk, and optimize costs. A reliable platform with dedicated human support.