By Olivia Dubois
·
April 21, 2026
Shadow IT is everywhere. Roughly 80% of employees use apps that were never approved by IT — creating security, compliance, and cost risk. Yet only a small fraction of enterprises have an accurate picture of what is really running in the browser, on cards, and in personal workspaces.
Outcome: fewer blind spots, lower incident probability, and measurable savings on duplicate and zombie subscriptions.
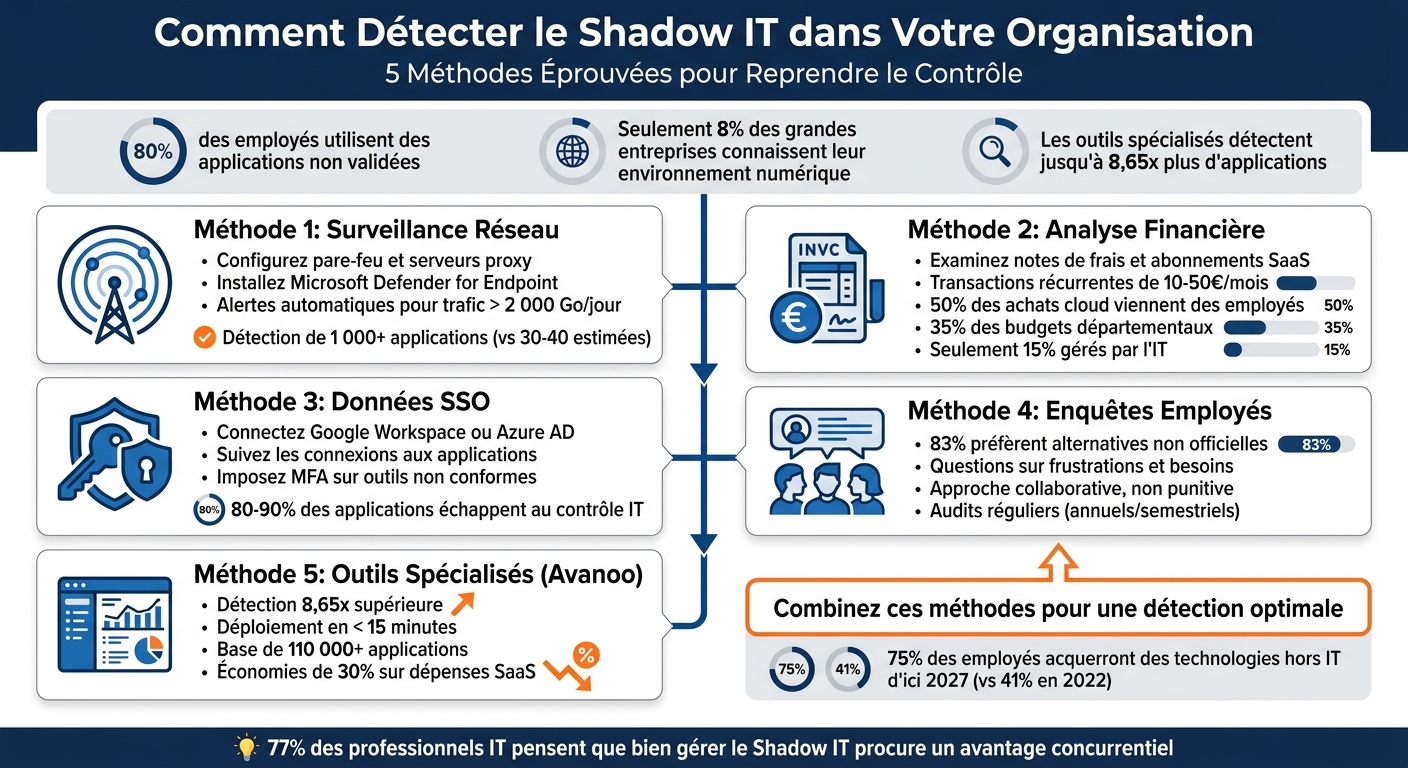
Forward firewall / proxy logs into a discovery tool, deploy endpoint agents, and tune policies such as “new high-volume SaaS” or “new popular consumer app.” Set thresholds (e.g. alert when an unknown destination exceeds 2 TB/day to unsanctioned storage). Many IT teams assume 30–40 cloud apps; real usage is often 1,000+ distinct services.
Unlike self-reported surveys, traffic shows behavior. Encrypted traffic still leaks metadata (SNI, DNS, timing). Combine with DPI where policy allows. Attack surface management tools often reveal 30–50% more external assets than teams knew existed.
"You can’t protect — or audit — what you don’t know exists." — Outpost24
Behavioral analytics catches scheduled uploads to personal drives and other exfil precursors. Integrate discovery with enforcement (block, warn, or route to approved alternatives).
About 50% of cloud purchases originate with employees, 35% with departments, and only 15% with central IT — so finance is a Shadow IT ledger. Connect discovery to tools like Spendesk or Pennylane and alert on recurring “software”, “subscription”, or “web services” categories that are not in your golden path.
Watch €10–€50/month recurring charges: classic Shadow IT “long tail.” ML classification helps triage ambiguous vendors.
Purchase orders sometimes hide SaaS inside broader statements of work. Compare purchased seats to real usage to find zombie renewals.
"Most organizations are surprised by how much Shadow IT they actually have… it’s not uncommon to discover 8–10× more SaaS accounts than they thought." — Lior Yaari, CEO, Grip Security
Build a renewal calendar from procurement data to stop silent auto-renewals.
SSO shows who authenticated to what — a strong signal for sanctioned apps. Pair it with HR attributes to find team-level sprawl. Watch OAuth scopes and risky consent grants.
Correlate discovered accounts to owners and business units. SSO often reveals 80–90% more unsanctioned apps than traditional CMDB inventories. When you find a risky app, use SSO to enforce MFA, step-up auth, or revoke access.
80% of employees admit using unapproved SaaS; 83% prefer a “good enough” unsanctioned tool over a mediocre official one. Position surveys as productivity improvements, not witch hunts. Ask: tool name, use case, team size, and data sensitivity.
"Punishing employees for Shadow IT only pushes the behavior further underground — increasing risk." — Grip Security
Cross-check survey answers with network, endpoint, and SSO evidence. Focus audits on GenAI, personal cloud storage, risky OAuth integrations, BYOD, and browser extensions. Gartner projects 75% of employees will acquire or create tech outside IT’s visibility by 2027 (vs 41% in 2022).

Avanoo stitches SSO + finance + browser signals so you see SaaS and Shadow AI (e.g. ChatGPT, Claude) even when purchases bypass IT. Deployment is typically <15 minutes to first insights.
In early 2026, a 15,000-user European audit firm used Avanoo for NIS2 readiness: 2,493 apps in use vs 200 officially tracked, 379 flagged as sensitive.
"We discovered 214 AI tools in the company. We only knew about 7. Avanoo gave us the clarity to act." — Thomas D., IT security lead, European bank
| Plan | Best for |
|---|---|
| Premium Diagnostic | Time-boxed risk and spend audit |
| Business | Continuous inventory + automated guidance |
| Enterprise | Large-scale integrations + dedicated support |
No single signal catches everything: SSO misses freemium and personal accounts; expenses miss free tools. The winning design is multi-source correlation plus automation (alerts, nudges, workflows). A CAC40 group improved visibility materially in March 2026 by combining SSO, expenses, extension telemetry, and surveys — see also the wild west of SaaS.
Avanoo’s SaaS governance assistant pushes contextual nudges in the browser so users move toward approved tools instead of hitting hard blocks.
"Avanoo gave us complete visibility into SaaS and AI usage, strengthened security, and helped optimize costs effectively."
Treat Shadow IT as a continuous cycle: discover, assess, rationalize, standardize — especially as Shadow AI accelerates.
Look for visibility gaps, spikes in unsanctioned SaaS domains, security incidents involving unknown tools, and misalignment between official stacks and what teams actually use on BYOD.
Start with network monitoring + SaaS discovery and a simple asset map. Add continuous monitoring so new tools don’t appear silently between annual audits.
Make approved tools easier than workarounds (procurement speed, better UX, training). Pair that with transparent policies and discovery that nudges — not punishes — by default.
Shadow AI Expert & Chief AI Officer
Olivia Dubois is Shadow AI Expert and Chief AI Officer at Avanoo. An HEC Paris graduate and former BCG consultant, she helps enterprises detect and govern Shadow AI and Shadow IT.
See how Avanoo can map your SaaS and AI landscape, reduce risk, and optimize costs. A reliable platform with dedicated human support.